Which adapter enables a computer system to exchange information with other systems on a local network?
#network interface card
2
What measurement is commonly associated with computer processing speed?
#hertz
3
Which computer component is considered the nerve center of the computer system and is responsible for processing all of the data within the machine?
#CPU
4
Why do servers often contain duplicate or redundant parts?
#Servers should be accessible at all times.
5
What are two benefits of connecting a laptop computer to a docking station? (Choose two.)
#An external monitor can be used.
#Alternate connectivity options may be available.
6
What characteristic of word processing software would make it a local application?
#The software is stored on the local hard drive.
7
A user plans to run multiple applications simultaneously on a computer. Which computer component is essential to accomplish this?
#RAM
8
What are two advantages of purchasing a preassembled computer? (Choose two.)
#usually a lower cost
#adequate for performing most general applications
9
Applications can be grouped into general use software or industry specific software. What are two examples of industry specific software? (Choose two.)
#an educational tool
#medical practice management software
10
What is the main storage drive used by servers, desktops, and laptops?
#hard drive
11
A user reports that a peripheral device that was installed correctly last week has not been functioning since the PC was booted today. All other PC functions are working properly. What are three things a service technician should do to solve the problem? (Choose three.)
#Use the testing functionality on the peripheral itself, if available.
#Disconnect all cables connected to the computer except those connected to the peripheral.
#Ensure that the peripheral is powered on.
12
What two functions does a UPS provide that a surge protector does not? (Choose two.)
#It provides backup power from an internal battery.
#It gives the user time to safely shut down the computer if the power fails.
13
Which component is designed to remove high-voltage spikes and surges from a power line so that they do not damage a computer system?
#surge suppressor
14
Because of the potentially dangerous voltage levels, which two devices should you not open unless you have been specifically trained to work on them? (Choose two.)
#monitor
#power supply
15
What can be used to prevent electrostatic discharge (ESD)?
#grounding strap
16
How many unique values are possible using a single binary digit?
#2
17
Administrators at a multicampus college need access to their schedules wherever the administrators go. Which computing device would be the most appropriate?
#PDA
18
Which two steps should be performed when installing a peripheral device? (Choose two.)
#Download and install the most current driver.
#Connect the peripheral using an appropriate cable or wireless connection.
19
How is a server different from a workstation computer?
#The server provides services to clients.
20
Which three terms describe different types of computers? (Choose three.)
#laptop
#desktop
#mainframe
21
In newer operating systems, how are system resources assigned by default when components are installed?
#dynamically assigned between the component and the operating system
1
Which method of interacting with an operating system involves typing commands at a command prompt?
#CLI
2
What occurs when computers are configured to receive their network configurations dynamically?
#Each computer requests configuration information from a server.
3
An operating system is severely damaged. All data on the partition needs to be deleted, and all application software must be reinstalled. Which installation method should be used to correct the problem?
#clean install
4
Which Windows file system is more likely to be used in an enterprise-level environment?
#NTFS
5
What are two ways that a user can interact with an operating system shell? (Choose two.)
#CLI
#GUI
6
Windows XP has a known problem with specific Intel processors. What is the best course of action to take in this situation?
#Download and install the Windows patch that fixes this problem.
7
The Lesson TaskMaster application from ChalkBoard has a problem. Every time the software is installed and loaded on a Windows XP-based Dell computer, and the moment something is typed followed by a tab, two tabs are inserted instead of one. What would be the best solution to this problem?
#Download, install, and apply a patch from ChalkBoard.
8
Which two statements are true about drive partitions? (Choose two.)
#Partitions are necessary in multi-boot installations.
#A hard drive can be divided into an operating system partition and a data partition.
9
What is the purpose of a default gateway?
#identifies the device that allows local network computers to communicate with devices on other networks
10
What Explorer menu option is used to determine the Windows XP version installed on a computer?
#Help
11
Which three resource specifications are given by the manufacturer to ensure that an operating system performs as designed? (Choose three.)
#required hard disk space
#processor type and speed
#recommended amount of RAM
12
Which three pieces of information must be specified on a computer to allow that computer to send and receive information across networks? (Choose three.)
#IP address
#subnet mask
#default gateway
13
Which Windows XP Automatic Update option allows you to select the time when a Windows update is executed?
#Automatic (recommended).
14
Which two items must be unique to each computer and cannot be duplicated on a network? (Choose two.)
#computer name
#IP address
15
Which two statements should be included in a pre-installation checklist when upgrading an operating system? (Choose two.)
#Verify that the hardware resources meet or exceed the published minimum requirements.
#Complete a full backup of all important files and data.
16
What two items are available from the About Windows option through the Windows Explorer Help menu? (Choose two.)
#the end-user license agreement
#the operating system version number
17
What are three characteristics of an operating system that is released under the GPL (GNU Public License)? (Choose three.)
#full access to source code
#software often available free
#support normally user-based and often free
18
Which statement is true about installing an operating system on computers in a networked environment?
#The computer name must be unique for all computers on the same network.
19
A computer in the Advanced Technology Center computer room on the second floor, room number 217, has the computer name ATC_217_7. What fact is true about the computer name?
#The name makes it easier for users to reference the device when connecting to it to share resources.
20
Which operating system patch installation method is used when a user is notified of a security update for remotely accessing a computer, but wishes not to install this patch?
#prompt for permission
1
Which two statements concerning networking standards are true? (Choose two.)
#provides consistent interconnections across networks
#simplifies new product development
2
Which two items are included in a network logical map? (Choose two.)
#naming scheme
#IP addressing scheme
3
What is a reason for disabling simple file sharing?
#It enables the user to set more specific security access levels.
4
Which address does an NIC use when deciding whether to accept a frame?
#destination MAC address
5
If the default gateway is configured incorrectly on the host, what is the impact on communications?
#The host can communicate with other hosts on the local network, but is unable to communicate with hosts on remote networks.
6

Refer to the graphic. What does the router do after it determines that a data packet from Network 1 should be forwarded to Network 2?
#It reassembles the frame with different MAC addresses than the original frame.
7
What is the function of the FCS field in an Ethernet frame?
#detects transmission errors
8
Host A needs to learn the MAC address of Host B, which is on the same LAN segment. A message has been sent to all the hosts on the segment asking for the MAC address of Host B. Host B responds with its MAC address and all other hosts disregard the request. What protocol was used in this scenario?
#ARP
9
What is a benefit of having a router within the distribution layer?
#keeps broadcasts contained within a local network
10
Which term is used to describe the process of placing one message format into another format so that the message can be delivered across the appropriate medium?
#encapsulation
11
Which table does a router use to make decisions about the interface through which a data packet is to be sent?
#routing table
12
Which two networking devices are used to connect hosts to the access layer? (Choose two.)
#hub
#switch
13
What does the 100 mean when referencing the 100BASE-T Ethernet standard?
#speed of transmission
14
What device is typically used as the default gateway for a computer?
#the router interface closest to the computer
15

Refer to the graphic. Five PCs are connected through a hub. If host H1 wants to reply to a message from host H2, which statement is true?
#H1 sends a unicast message to H2, but the hub forwards it to all devices.
16
Which type of address is used in an Ethernet frame header?
#MAC addresses only
17
A switch receives a frame with a destination MAC address that is currently not in the MAC table. What action does the switch perform?
#It floods the frame out of all active ports, except the origination port.
18
Which device accepts a message on one port and always forwards the message to all other ports?
#hub
19
What type of route allows a router to forward packets even though its routing table contains no specific route to the destination network?
#default route
20
An integrated router can normally perform the functions of which two other network devices? (Choose two.)
#switch
#wireless access point
21
What is the purpose of logical addresses in an IP network?
#They are used to determine which host device accepts the frame.
1
Which definition describes the term Internet?
#a network of networks that connects countries around the world
2
What type of connection point is a point of presence (POP)?
#between an ISP and a home-based LAN
3
What is the term for the group of high-speed data links that interconnect ISPs?
#Internet backbone
4
What are three characteristics of business class ISP service? (Choose three.)
# fast connections
# extra web space
# additional e-mail accounts
5
What does the tracert command test?
#the network path to a destination
6
What is a major characteristic of asymmetric Internet service?
#Upload speeds and download speeds are different.
7
Which three elements are required to successfully connect to the Internet? (Choose three.)
#an IP address
#a network connection
#access to an Internet service provider
8
Which two places are most appropriate to use UTP cabling? (Choose two.)
# in a home office network
# inside a school building
9
Which device can act as a router, switch, and wireless access point in one package?
#ISR
10
What type of end-user connectivity requires that an ISP have a DSLAM device in their network?
#digital subscriber line technology
11
Why would an ISP require a CMTS device on their network?
#to connect end users using cable technology
12

Refer to the graphic. What type of cabling is shown?
#fiber
13

Refer to the graphic. What type of cabling is shown?
#UTP
14
Which two characteristics describe copper patch panels? (Choose two.)
#uses RJ-45 jacks
#allows quick rearrangements of network connections
15
What term describes each router through which a packet travels when moving between source and destination networks?
#hop
16
What does adherence to cabling standards ensure?
# reliable data communications
17
What connector is used to terminate Ethernet unshielded twisted pair (UTP) cabling?
# RJ-45
18
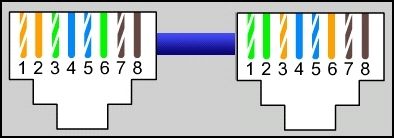
Refer to the graphic. What type of cable is shown?
#crossover
19
What are two advantages of cable management? (Choose two.)
#aids in isolation of cabling problems
#protects cables from physical damage
20
What are two common causes of signal degradation when using UTP cabling? (Choose two.)
#having improper termination
#using low quality cables or connectors
21
What are three commonly followed standards for constructing and installing cabling? (Choose three.)
#pinouts
#cable lengths
#connector types
1
Which two statements describe packets that are sent through a Linksys integrated router using NAT? (Choose two.)
#Packets that are sent to a destination outside the local network need to be translated.
#Packets that are sent between hosts on the same local network do not need to be translated.
2
A PC obtains its IP address from a DHCP server. If the PC is taken off the network for repair, what happens to the IP address configuration?
#The address is returned to the pool for reuse when the lease expires.
3
What is the destination MAC address in a multicast Ethernet frame?
#an address that begins with 01-00-5E in hexadecimal
4
How many bits are available for Class B host IP addresses using a default subnet mask?
#16
5
Which default subnet mask provides the most host bits?
#255.0.0.0
6

Refer to the graphic. NAT and DHCP are installed on the Linksys integrated router. Which IP address is most likely to be assigned to the local computer, Host1?
#10.0.0.17
7

Refer to the graphic. The host requests an IP configuration from the Linksys integrated router which is configured to provide DHCP services. In addition to the host IP address, which additional IP address is provided that will allow the host to access the ISP and the Internet?
#internal IP address of the integrated router that connects to the local network
8

Refer to the graphic. A user at the workstation cannot connect to the server. All cables have been tested and are working and all devices have IP addressing. However, the user cannot ping the server. What is causing the problem?
#The workstation and server are on different logical networks.
9
Which part of an IP address identifies a specific device on a network?
#host portion
10
Which type of server dynamically assigns an IP address to a host?
#DHCP
11
What is one of the purposes of NAT?
#prevents external users from detecting the IP addresses used on a network
12
Assuming a default mask, which portion of the IP address 175.124.35.4 represents the host?
#35.4
13
How large are IPv4 addresses?
#32 bits
14
Which statement is true concerning private IP addresses?
#solves the issue of a finite number of available public IP addresses
15
Yvonne is talking to her friend on the phone. What type of message is this?
#unicast
16
Which of the following are private IP addresses? (Choose three.)
#10.1.1.1
#172.16.4.4
#192.168.5.5
17
Which three statements describe a DHCP Discover message? (Choose three.)
#The destination IP address is 255.255.255.255.
#The message comes from a client seeking an IP address.
#All hosts receive the message, but only a DHCP server replies.
18
What destination IP address is used in a unicast packet?
#a specific host
19
How many usable hosts are available given a Class C IP address with the default subnet mask?
#254
20
What information must be included within a unicast message for it to be delivered on an Ethernet network?
#MAC and IP addresses that correspond to a specific destination host
21
A host with the IP address 172.32.65.13 and a default mask belongs to what network?
#172.32.0.0
1
What is the correct order of the layers of the OSI reference model, starting at the lowest layer and working up the model?
#physical, data link, network, transport, session, presentation, application
2
What three items are contained in an Ethernet header and trailer? (Choose three.)
#source MAC address
#destination MAC address
#error-checking information
3
Which protocols are TCP/IP application layer protocols? (Choose two.)
#FTP
#SMTP
4

Refer to the graphic. Which protocol is used to access this website?
#HTTP
5
What is an advantage of the use of layers in the OSI reference model?
#It prevents changes in one layer from affecting other layers.
6
What term is used to describe how TCP/IP protocols are layered and interact to format, address, and transmit information across a network?
#protocol stack
7
Whenever e-mail clients send letters, what device is used to translate the domain names into their associated IP addresses?
#DNS server
8
An Internet server is running both FTP and HTTP services. How does the server know which of these applications should handle an incoming segment?
#The segment destination port number identifies the application that should handle it.
9
You are creating a network-based video game. What influences your decision about which transport protocol to use for the application?
#UDP will not disrupt the game to retransmit dropped packets.
10
Which port number is used by SMTP?
#25
11
Which application is most likely used to translate www.cisco.com to 198.133.219.25?
#DNS
12
Which of the following are layers of the TCP/IP model? (Choose three.)
#Application
#Internet
#Network Access
13
Which protocol is used by e-mail servers to communicate with each other?
#SMTP
14
What client software enables logged in users to communicate with other logged in users in real time?
#instant messaging
15
What type of server would use IMAP?
16
What resolves a website URL to an IP address?
#DNS server
17
What information is contained in an IP header?
#source and destination IP addresses
18
Which protocol is used by FTP to transfer files over the Internet?
#TCP
19
A client has decoded a frame and started the de-encapsulation process. In which order does the de-encapsulation process occur?
1) remove Ethernet header and trailer
2) remove IP header
3) remove TCP header
4) pass data to the application
20
A device receives an Ethernet frame and recognizes the MAC address as its own. What does the device do to the message to get to the encapsulated data?
#removes the Ethernet header and trailer
21
Cabling issues are associated with which OSI layer?
#1
22
A network client in a corporate environment reboots. Which type of server would most likely be used first?
#DNS
1
Complete the following sentence: WEP is used to ______ , and EAP is used to _____ wireless networks.
#encrypt; authenticate users on
2
What are three advantages of wireless over wired technology? (Choose three.)
#anytime, anywhere connectivity
#ease of adding additional devices
3
A technician has been asked to provide wireless connectivity to the wired Ethernet network of a building. Which three factors affect the number of access points needed? (Choose three.)
#the size of the building
#the number of solid interior walls in the building
#the presence of microwave ovens in several offices
4
Which statement is true concerning wireless bridges?
#connects two networks with a wireless link
5

Refer to the graphic. In the Wireless menu option of a Linksys integrated router, what does the Network Mode option Mixed mean?
#The router supports 802.11b, 802.11g, and 802.11n devices.
6
Why is IEEE 802.11 wireless technology able to transmit further distances than Bluetooth technology?
#has higher power output
7
Which statement is true concerning an ad-hoc wireless network?
#created by connecting wireless clients in a peer-to-peer network
8
What is the difference between using open authentication and pre-shared keys?
#Pre-shared keys require an encrypted secret word. Open authentication does not require a secret word.
9
Which statement is true about open authentication when it is enabled on an access point?
#requires no authentication
10
Which WLAN component is commonly referred to as an STA?
#wireless client
11
Which two statements about a service set identifier (SSID) are true? (Choose two.)
#tells a wireless device to which WLAN it belongs
#all wireless devices on the same WLAN must have the same SSID
12
Why is security so important in wireless networks?
#Wireless networks broadcast data over a medium that allows easy access.
13
What term describes the encoding of wireless data to prevent intercepted data from being read by a hacker?
#encryption
14
What type of authentication do most access points use by default?
#Open
15
What are two authentication methods that an access point could use? (Choose two.)
#EAP
#pre-shared keys
16
What are two benefits of wireless networking over wired networking? (Choose two.)
#mobility
#reduced installation time
17

Refer to the graphic. In the Wireless menu of a Linksys integrated router, what configuration option allows the presence of the access point to be known to nearby clients?
#SSID Broadcast
18
What are the two WEP key lengths? (Choose two.)
#64 bit
#128 bit
19
Which two statements characterize wireless network security? (Choose two.)
#With SSID broadcast disabled, an attacker must know the SSID to connect.
#Using the default IP address on an access point makes hacking easier.
20
What does the Wi-Fi logo indicate about a wireless device?
#The device is interoperable with other devices of the same standard that also display the Wi-Fi logo.
21
What access-point feature allows a network administrator to define what type of data can enter the wireless network?
#traffic filtering
1
Identify three techniques used in social engineering. (Choose three.)
#vishing
#phishing
#pretexting
2
A flood of packets with invalid source-IP addresses requests a connection on the network. The server busily tries to respond, resulting in valid requests being ignored. What type of attack occurred?
#SYN flooding
3
While surfing the Internet, a user notices a box claiming a prize has been won. The user opens the box unaware that a program is being installed. An intruder now accesses the computer and retrieves personal information. What type of attack occurred?
#Trojan horse
4
What is a major characteristic of a Worm?
#exploits vulnerabilities with the intent of propagating itself across a network
5
During a pretexting event, how is a target typically contacted?
#by phone
6
What term is used to describe a dedicated hardware device that provides firewall services?
#appliance-based
7

Refer to the graphic. In the Linksys Security menu, what does the SPI Firewall Protection option Enabled provide?
#It requires that packets coming into the router be responses to internal host requests.
8
Many best practices exist for wired and wireless network security. The list below has one item that is not a best practice. Identify the recommendation that is not a best practice for wired and wireless security.
#Disable the wireless network when a vulnerability analysis is being performed.
9
What environment would be best suited for a two-firewall network design?
#a large corporate environment
10
Which statement is true about port forwarding within a Linksys integrated router?
#Only external traffic that is destined for specific internal ports is permitted. All other traffic is denied.
11
Which two statements are true concerning anti-spam software? (Choose two.)
#When anti-spam software is loaded, legitimate e-mail may be classified as spam by mistake.
#Even with anti-spam software installed, users should be careful when opening e-mail attachments.
12
What type of advertising is typically annoying and associated with a specific website that is being visited?
#popups
13
To which part of the network does the wireless access point part of a Linksys integrated router connect?
#internal
14
What statement is true about security configuration on a Linksys integrated router?
#Internet access can be denied for specific days and times.
15
Which abbreviation refers to an area of the network that is accessible by both internal, or trusted, as well as external, or untrusted, host devices?
#DMZ
16
Which statement is true regarding anti-virus software?
#Only after a virus is known can an anti-virus update be created for it.
17
What is one function that is provided by a vulnerability analysis tool?
#It identifies missing security updates on a computer.
18
What part of the security policy states what applications and usages are permitted or denied?
#acceptable use
19
What best practice relates to wireless access point security?
#a change of the default IP address
20
What is a widely distributed approach to marketing on the Internet that advertises to as many individual users as possible via IM or e-mail?
#spam
1
A technician is unsuccessful in establishing a console session between a PC and a Linksys integrated router. Both devices have power, and a cable is connected between them. Which two troubleshooting steps could help to diagnose this problem? (Choose two.)
#Ensure the correct cable is used.
#Ensure the link status LED on the integrated router is lit.
2
Identify two physical-layer network problems. (Choose two.)
#hardware failure
#loose cable connections
3
Only one workstation on a particular network cannot reach the Internet. What is the first troubleshooting step if the divide-and-conquer method is being used?
#Check the workstation TCP/IP configuration.
4
Which two troubleshooting techniques are suitable for both home networks and large corporate networks? (Choose two.)
#documenting the troubleshooting process
#keeping a record of system upgrades and software versions
5
What two items could be checked to verify connectivity between the router and the ISP? (Choose two.)
#router status page
#connectivity status as indicated by LEDs
6
When acting as a DHCP server, what three types of information can an ISR provide to a client? (Choose three.)
#default gateway
#dynamic IP address
#DNS server address
7
A customer called the cable company to report that the Internet connection is unstable. After trying several configuration changes, the technician decided to send the customer a new cable modem to try. What troubleshooting technique does this represent?
#substitution
8
Which troubleshooting method begins by examining cable connections and wiring issues?
#bottom-up
9
What command is used to determine the location of delay for a packet traversing the Internet?
#tracert
10
A technician suspects that a Linksys integrated router is the source of a network problem. While troubleshooting, the technician notices a blinking green activity LED on some of the ports. What does this indicate?
#The ports are operational and are receiving traffic.
11
Which three settings must match on the client and access point for a wireless connection to occur? (Choose three.)
#SSID
#authentication
#encryption key
12
What should a network administrator do first after receiving a call from a user who cannot access the company web server?
#Ask the user what URL has been typed and what error message displays.
13

Refer to the graphic. What configuration is incorrect in the network shown?
#The wired connection is the wrong type of cable.
14
A technician is troubleshooting a security breach on a new wireless access point. Which three configuration settings make it easy for hackers to gain access? (Choose three.)
#broadcasting the SSID
#using open authentication
#using the default internal IP address
15

Refer to the graphic. What configuration is incorrect in the network shown?
#The host IP address is incorrect.
16
Typically, help desk personnel assist end users in which two tasks? (Choose two.)
#identifying when the problem occurred
#implementing the solution to the problem
17
Network baselines should be performed in which two situations? (Choose two.)
#after the network is installed and running optimally
#after major changes are implemented on the network
18
Which two items should be added to the documentation following a troubleshooting event? (Choose two.)
#final resolution
#results of successful and unsuccessful troubleshooting steps
19
A PC is plugged into a switch and is unable to connect to the network. The UTP cable is suspected. What could be the problem?
#A crossover cable is being used.
20
Which ipconfig command requests IP configuration from a DHCP server?
#ipconfig /renew
21

Refer to the graphic. The wireless host cannot access the Internet, but the wired host can. What is the problem?
#The host WEP key is incorrect.
22
How does remote-access software help in the troubleshooting process?
#Diagnostics can be run without a technician being present at the site.
23
What command is used to determine if a DNS server is providing name resolution?
#nslookup

